third Celebration Danger Administration
,
Breach Notification
,
Enterprise Continuity Administration / Catastrophe Restoration
Investigations Ongoing, However Operations Reportedly Not Affected
Automotive know-how and components provider Denso has confirmed to ISMG that it fell sufferer to a ransomware assault final week. Investigations are ongoing. The corporate has not disclosed particulars of the ransom demanded or the operator behind the assault, however the unbiased darkish internet monitoring platform DarkTracer says the assault is the work of the Pandora ransomware group.
See Additionally: Webinar | Stop, Detect & Restore: Information Safety Backup Programs Made Straightforward
A spokesperson for Denso tells ISMG {that a} “group firm in Germany’s community was illegally accessed by a 3rd celebration on March 10, 2022, and sure, it was a ransomware assault.” Denso, a provider to and previously a part of the Japanese Toyota Group auto producer, says it has knowledgeable all respective legislation enforcement departments and a specialised cybersecurity company to additional examine the incident.
An organization assertion says, “After detecting the unauthorized entry, Denso promptly minimize off the community connection of units that obtained unauthorized entry and confirmed that there isn’t any impression on different DENSO services.”
A Denso spokesperson instructed ISMG, “There isn’t a interruption to manufacturing actions and we preserve working all our crops as common. We [could] do that as a result of we transferred the operation which is impacted by this incident to different Denso websites. We’re investigating which information was impacted by this incident. We can not say any additional particulars about it.”
DarkTracer Claims Pandora Group Is Accountable
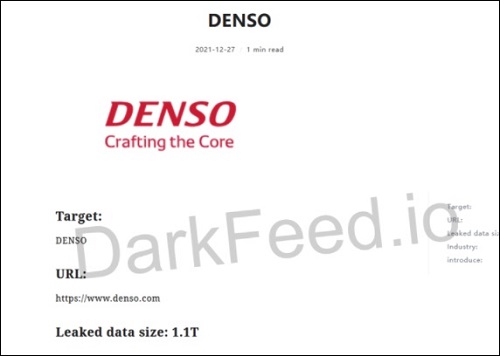
Though the Denso spokesperson declined to reveal particulars concerning the ransomware operators, an unbiased deep and darkish internet on-line monitoring platform known as DarkTracer tweeted that the Pandora ransomware group has claimed accountability for the assault and is about to launch the information publicly on Wednesday if its calls for will not be met.
[ALERT] Pandora gang has introduced “DENSO” on the sufferer listing. pic.twitter.com/kh9wzGV1io
— DarkTracer : DarkWeb Legal Intelligence (@darktracer_int) March 13, 2022
The Pandora group claims to have 1.4TB of knowledge, consisting of greater than 157,000 items of knowledge, together with buy orders and technical drawings. In response to those claims, the Denso spokesperson clarified that the corporate can not disclose the title of the third celebration and/or touch upon their demand matters due to the impression it might have on the investigation.
DarkTracer has additionally shared an indicator of compromise of the Pandora ransomware group that it says has not simply attacked Denso, but in addition many different main Japanese firms.
It is a IoC of Pandora ransomware, which attacked main Japanese firms.
malware:5b56c5d86347e164c6e571c86dbf5b1535eae6b979fede6ed66b01e79ea33b7b pic.twitter.com/wuyis3xbiT
— DarkTracer : DarkWeb Legal Intelligence (@darktracer_int) March 14, 2022
DarkTracer didn’t instantly reply to ISMG’s request to establish the opposite focused organizations in Japan, however a dwell ransomware monitoring service supplier platform DarkFeed, has listed Japan’s identified silicon wafer producer International Wafers Japan in its listing of these focused by the Pandora group on Saturday.
International Wafers Japan has not but responded to ISMG’s request for a remark concerning these claims.
Not the First Time
In accordance with an earlier report from native Japanese information company The Asahi Shimbun, Denso’s Mexico unit was the goal of a ransomware assault by a bunch known as Rook in December 2021. Rook claimed to have stolen 1.1TB of knowledge from Denso, together with the personally identifiable data of Denso’s Mexican plant employees.
The information company cited a supply from Denso saying that round 20 computer systems used within the Mexico plant that had been related to an outdated community had been breached. However all essential information required for continuity of enterprise operations at that plant had already been transferred to a brand new laptop community, which helped Denso resume its Mexican plant operations by Jan. 3, 2022.
No data on the cost of a ransom was recorded from Denso at the moment, however a posting on Rook’s web site disappeared on Jan. 4 – a day after the operations resumed in Mexico, the information company says.
Toyota’s Suppliers Beneath the Radar
Toyota Motor Corp., one of many largest vehicle producers in Japan, has lengthy been on the radar of ransomware operators, however primarily by way of its third-party provide chain suppliers. On Feb. 28, one other third-party provider and a producing companion of Toyota – Kojima Industries Corp., – suffered a cyberattack that compelled Toyota to droop its operations in any respect of its 28 manufacturing traces in Japan on March 1, 2022 (see: Replace: Toyota to Resume Ops After Cyberattack Scare).
The suspension of providers from Toyota and its subsidiaries affected the manufacturing of round 10,000 vehicles, which is 5% of Toyota’s month-to-month output in Japan.